Imagine you are checking into a hotel in a foreign city after a fourteen-hour flight. Instead of standing at a desk presenting a physical passport to a stranger who will then photocopy it and store it in a poorly secured local database, you simply walk toward the elevator. Your Digital Agent has already negotiated with the hotel’s system. It proved your identity, verified your payment capability, and confirmed your age without ever revealing your actual birth date or credit card number. By the time you reach your room, your phone has been issued a cryptographic key that only your biometrics can activate.
This is the promise of Agentic Identity. It represents a fundamental shift from identity as a static record to identity as a proactive, intelligent representative.
What is Agentic Identity?
To understand the agentic future, we must look at the inadequacy of the present. Today, digital identity is administrative and fragmented. You are a collection of accounts owned by Google, Microsoft, your employer, and your bank. You do the heavy lifting of logging in, managing passwords, and consenting to data harvesting.
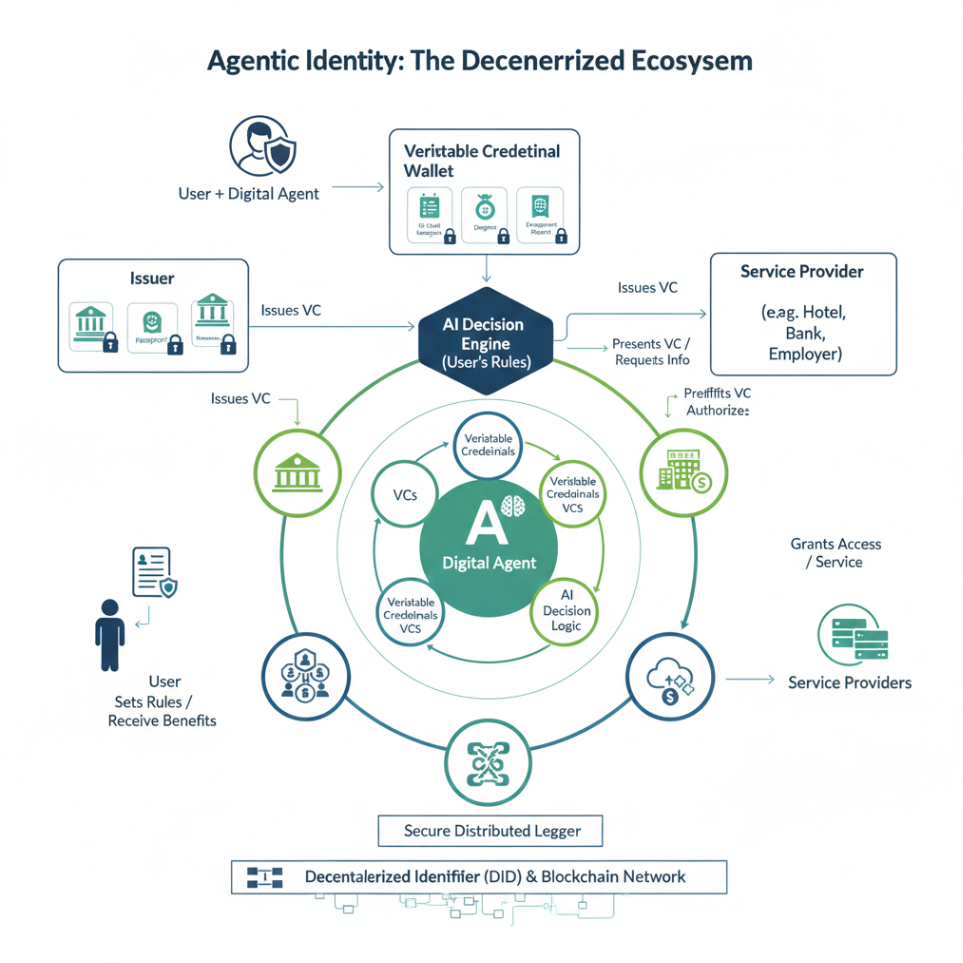
Agentic Identity flips this model. It is a paradigm where an autonomous software agent acts on your behalf. This agent is powered by three converging technologies:
- Decentralized Identifiers (DIDs): These are digital addresses that you own and control, rather than being “loaned” to you by a corporation.
- Verifiable Credentials (VCs): These are the digital equivalent of a physical wallet. They are tamper-proof, cryptographically signed proofs of information, such as a driver’s license, a university degree, or an employment status, that can be verified instantly without contacting the issuer.
- Agentic AI: This is the brain. It is an AI trained to understand your preferences, legal boundaries, and security requirements. It doesn’t just store data; it makes decisions about when and how to share it.
The Agentic identity environment is not a technology or a product. It is an ecosystem that relies on the ongoing evolution of technology and identity management.
Why It Matters and Why It’s Quiet
For the executive, this is about shifting from managing users to managing trusted relationships. Currently, every time a customer or employee interacts with your system, there is “friction.” Friction costs money, reduces security, and frustrates humans. Agentic identity removes the friction by allowing machines to handle the “trust” part of the equation.
The reason most people haven’t heard of it is that identity is often viewed as “plumbing.” It isn’t a flashy product feature; it is infrastructure. Furthermore, the current gatekeepers of identity (the massive social and search platforms) benefit from the current centralized model. They have little incentive to promote a technology that gives users the keys to their own data.
The Foundation: Getting Your House in Order
You cannot deploy an autonomous agentic strategy if your current Identity and Access Management (ICAM) is a mess. It is like trying to install a high-end home automation system when your house has faulty wiring and a leaky roof.
Before we can move into the world of blockchain-based, agentic identity, an enterprise must master the “Identity Journey.”
Phase | Focus | Purpose |
Legacy ICAM | Passwords and Perimeters | Basic gatekeeping. |
Cloud-Native ICAM | SSO and MFA | Centralizing access in the cloud. |
Zero Trust | Continuous Verification | Assuming the network is already breached. |
Agentic Identity | Decentralized Autonomy | Delegating trust to intelligent agents. |
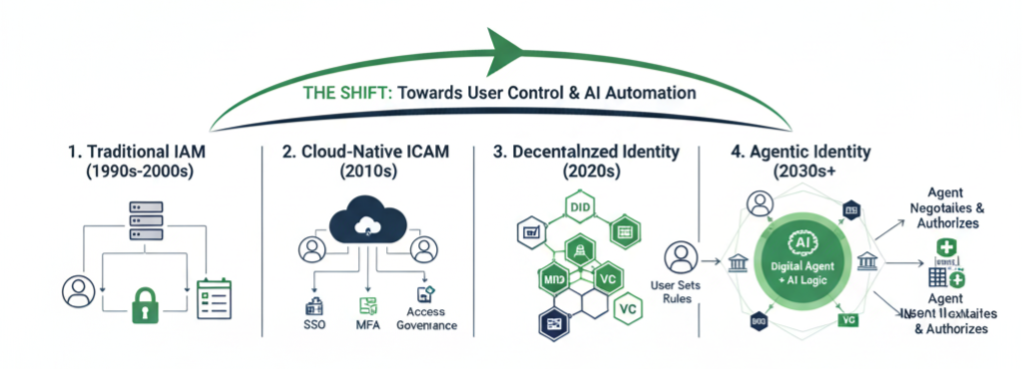
If your organization still struggles with “orphaned” accounts from employees who left three years ago, or if you still rely on SMS-based passwords, you are not ready for agents. An agent can only be as effective as the policies it is programmed to follow. If your internal data governance is weak, an agent will simply automate your vulnerabilities at the speed of light.
Cybersecurity and the Reduced Blast Radius
From a security perspective, Agentic Identity is a dream. In our current centralized world, identity providers are “honeypots.” If an attacker breaches a major identity provider, they get the keys to millions of kingdoms.
In an agentic model, there is no central honeypot. Each identity is decentralized. If an attacker wants to steal identities, they have to attack individuals one by one. This significantly reduces the blast radius of a breach. Furthermore, agents utilize “Just-In-Time” access. They don’t hold permanent permissions; they request a specific credential for a specific task and then discard it. This is the ultimate expression of the Principle of Least Privilege. Sound suspiciously familiar? It should. Agentic identity builds on the foundation of modern ICAM and enhances it.
The Realistic Path to Preparation
We are moving away from the era of “Human-in-the-Loop” for every digital interaction. As an executive, you should not be looking for an “Agentic Identity App” to buy today. Instead, you should be preparing your architecture for “Agentic Compatibility.”
- Audit Your Identity Debt: Clean up your current ICAM. If your HR system doesn’t automatically trigger identity revocation in your IT system, fix that first. Automated agents require automated foundations.
- Demand Interoperability: When vetting new vendors, ask about their support for W3C standards like DIDs and Verifiable Credentials. Avoid “proprietary islands” that lock your data into a single vendor’s ecosystem.
- Move Toward Attribute-Based Access: Stop thinking in terms of “Bob has access to the Finance folder.” Start thinking in terms of “Anyone with a ‘Finance Manager’ credential can access this folder.” This shift from identity-based to attribute-based access is the language that agents speak.
- Invest in Privacy-Preserving Tech: Explore technologies like Zero-Knowledge Proofs (ZKP). This allows an agent to prove something is true (e.g., “The user is over 18”) without revealing the underlying data (e.g., the user’s date of birth).
The agentic future is not a far-off sci-fi concept; it is the logical conclusion of the AI and Blockchain revolutions. It offers a world where we spend less time proving who we are and more time doing what we intended to do. The question for your enterprise is whether you will be the one providing the trusted credentials that these agents rely on, or if you will be left behind in the world of manual logins and data breaches.
Allen Firouz
Identity Evangelist – Hekima Solutions
Sources:
https://thefutureidentity.com/the-state-of-digital-identity-in-north-america/
https://www.w3.org/TR/did-1.1/
https://auth0.com/blog/what-are-verifiable-credentials-why-you-should-care/


